Web UI SSO is for human users accessing the hosted UI and is separate from Documents API authentication.
What you’ll set up
You will create a non-gallery Enterprise Application in Microsoft Entra ID and configure it for SP-initiated SAML SSO to the Resistant Documents Web UI. At the end you will have:- SAML SSO working end-to-end (login redirect → assertion → Web UI session)
- Required user claims mapped (
email,firstName,lastName) - Optional role mapping via
documents_roles(if used)
Prerequisites
Before you begin, ensure you have:- An active Resistant AI subscription / tenant
- An active Microsoft Entra ID tenant
- An Entra administrator account that can create Enterprise Applications
- Cloud Application Administrator
- Application Administrator
- Global Administrator
Testing vs Production
Testing and production Web UI tenants are separate.- You typically configure two Enterprise Applications in Entra: one for Testing and one for Production
- Users must be assigned separately for each environment
- Resistant AI will provide environment-specific Entity ID and ACS (Reply URL) values
Step 1 — Request configuration values from Resistant AI
Ask Resistant AI to provide the SAML configuration values required for your environment(s). These typically include:- Identifier (Entity ID / Audience URI)
- Reply URL (ACS URL)
- Sign-on URL (your Web UI entry URL)
- (Optional) SP metadata XML (recommended for import)
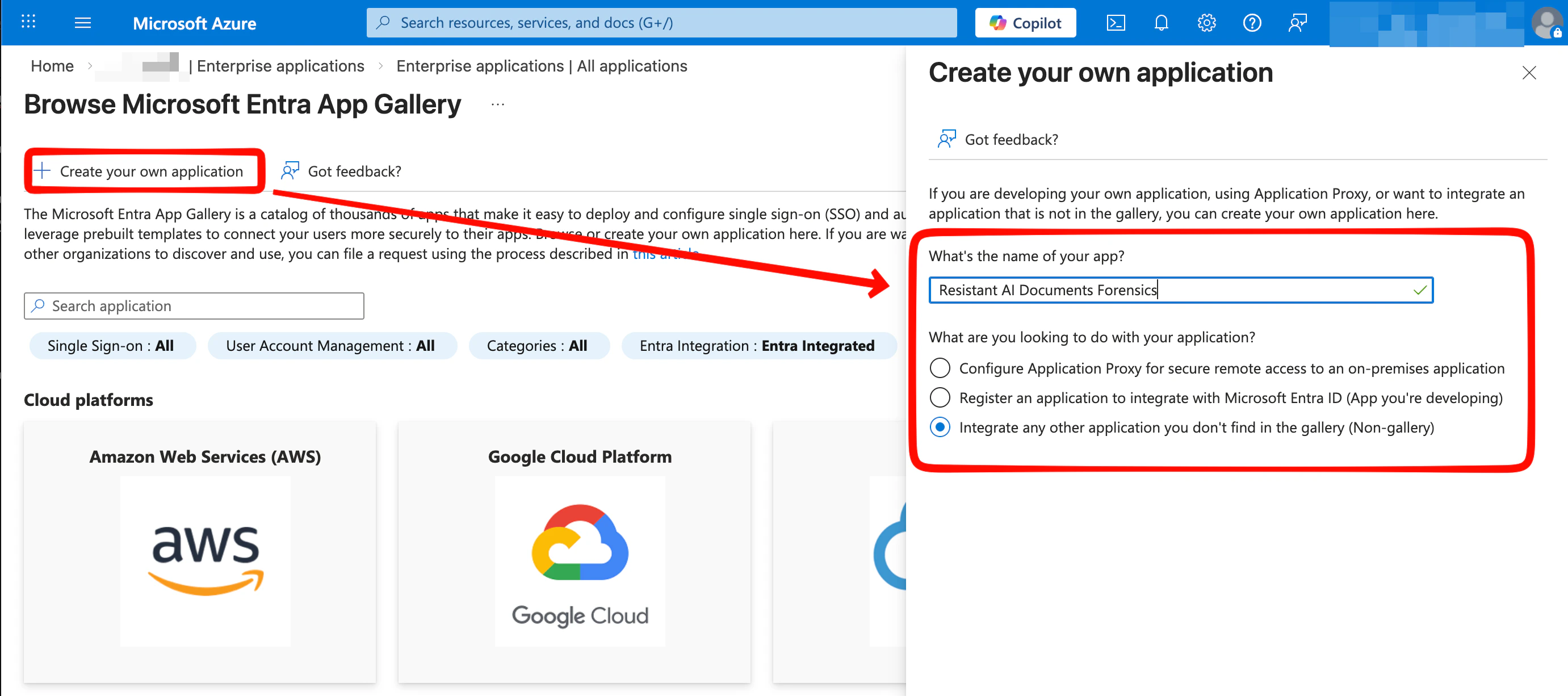
Step 2 — Create a custom (non-gallery) Enterprise Application
- Sign in to the Azure portal and open Microsoft Entra ID.
- Go to Enterprise applications → New application.
- Select Create your own application.
- Enter an application name (example: Resistant AI Document Forensics).
- Select Integrate any other application you don’t find in the gallery (Non-gallery).
Step 3 — Configure basic SAML settings
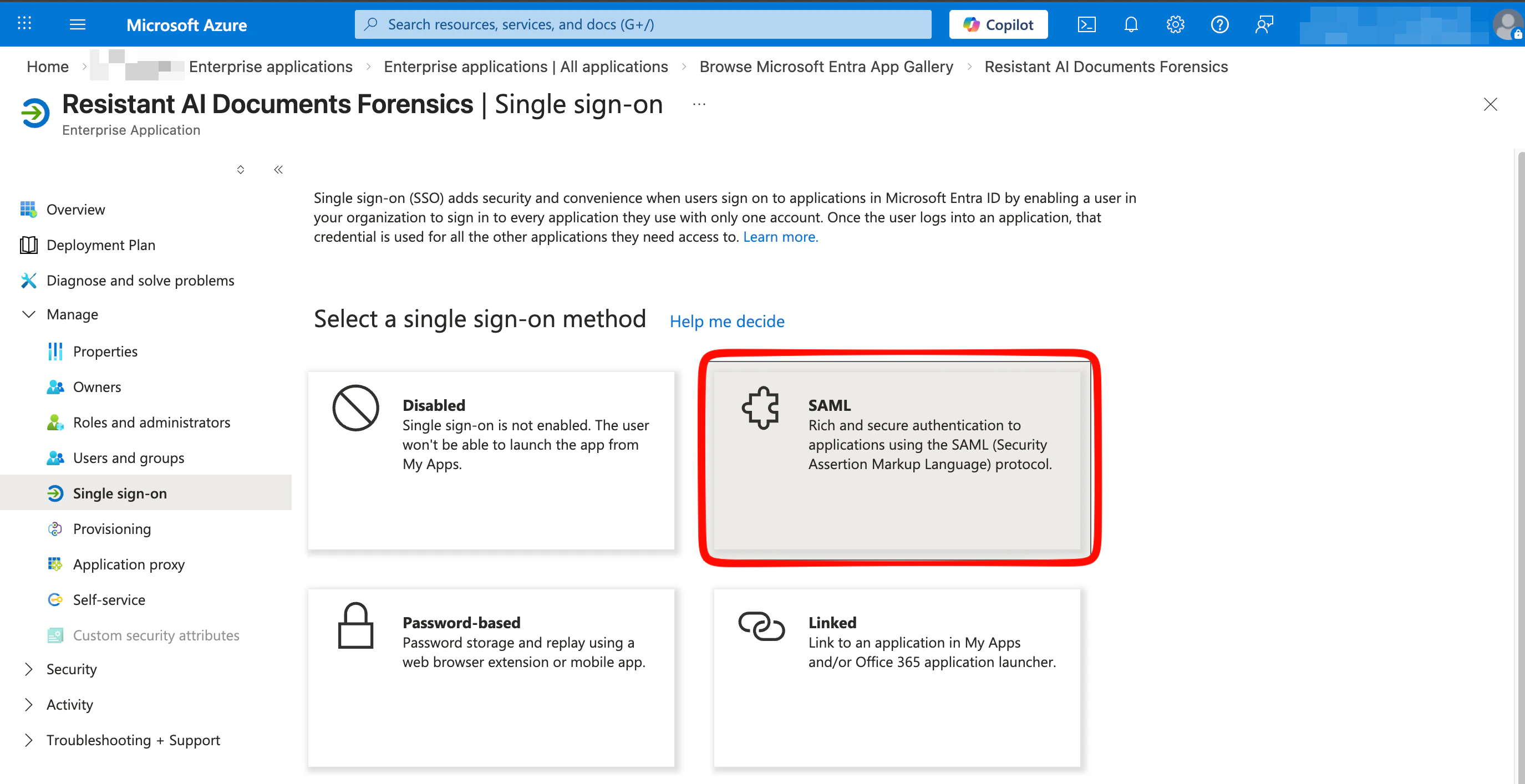
In the new enterprise application:- Open Overview and select Set up single sign on, or go to Manage > Single sign-on.
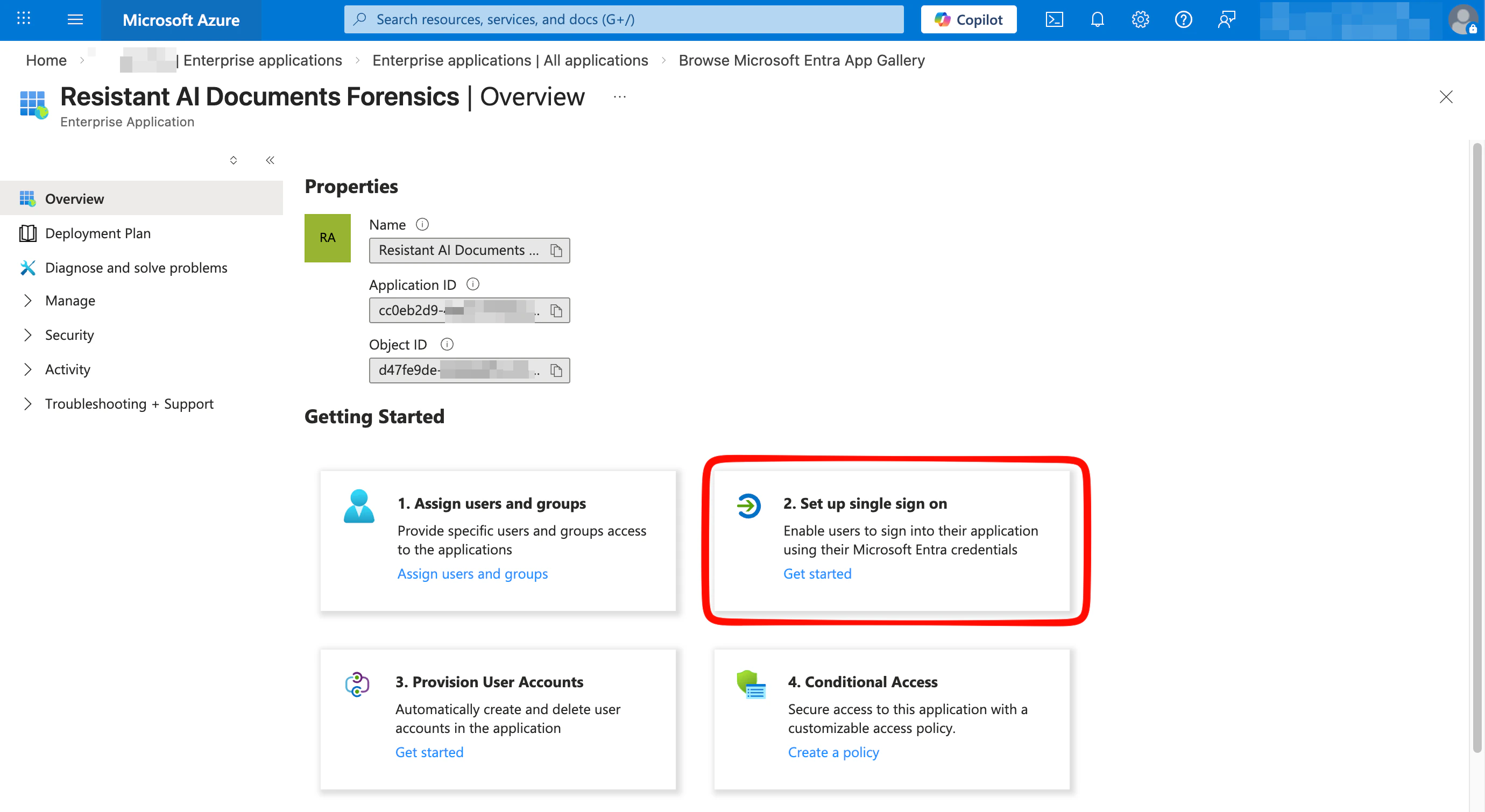
- Select SAML as the single sign-on method.
- Import the key SAML parameters from the metadata XML file provided by Resistant AI:
- Select Upload metadata file
- Choose the Metadata XML file
- Select Add
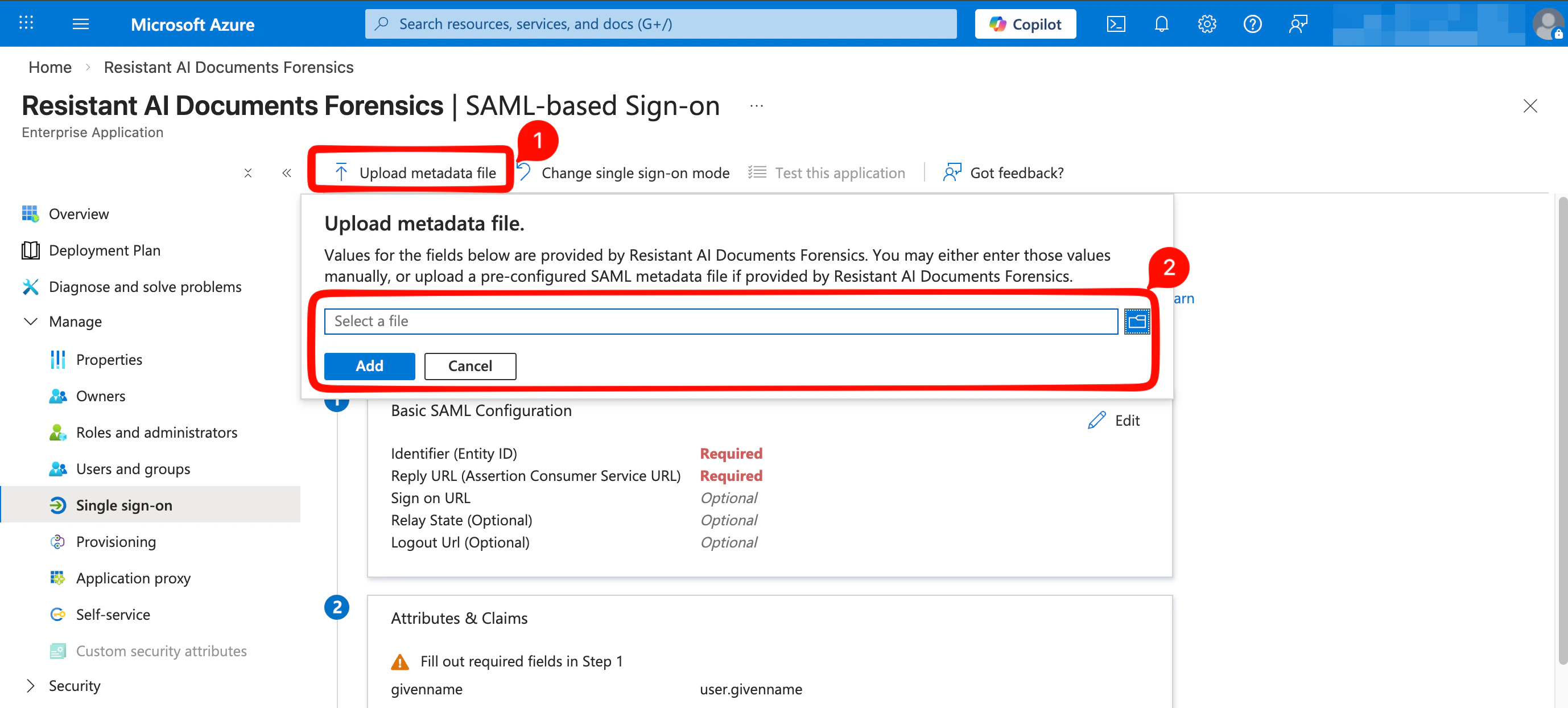
- Review the prefilled values in Basic SAML Configuration:
- Confirm that Identifier and Reply URL match the values provided by Resistant AI
- Enter the Sign-on URL using your Resistant AI Document Forensics UI URL
- Select Save, then close the dialog
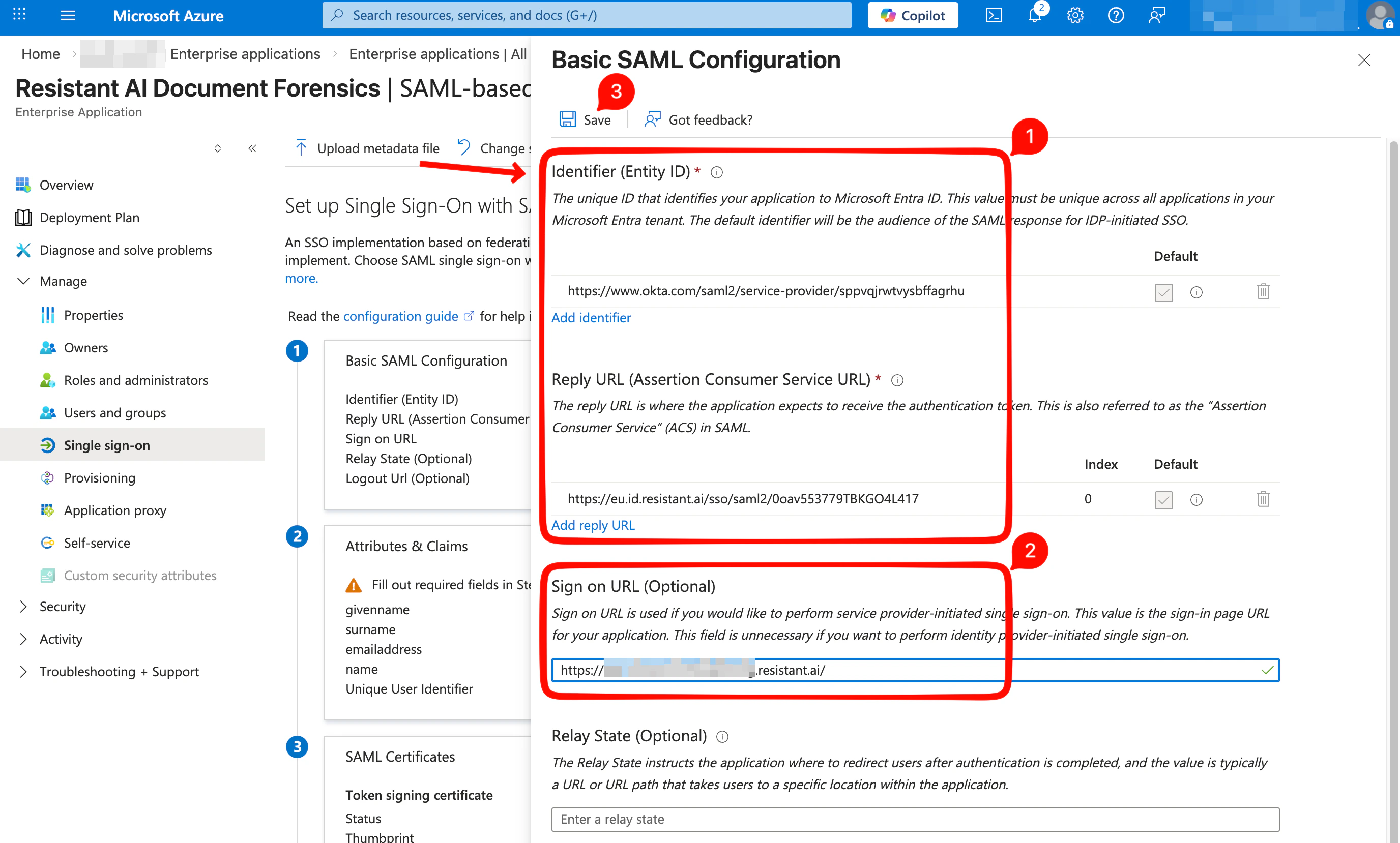
- If Microsoft Entra ID offers to test the SSO integration at this stage, select No, I’ll test later.
Step 4 — Configure attributes and claims
Microsoft Entra ID must send the required user profile attributes with each successful SSO login.| Required? | Claim name | Source attribute | Data type | Namespace | Name format |
|---|---|---|---|---|---|
| yes | user.mail | string | empty | Omitted (default) | |
| yes | firstName | user.givenname | string | empty | Omitted (default) |
| yes | lastName | user.surname | string | empty | Omitted (default) |
| no | documents_roles | varies | array of strings | empty | Omitted (default) |
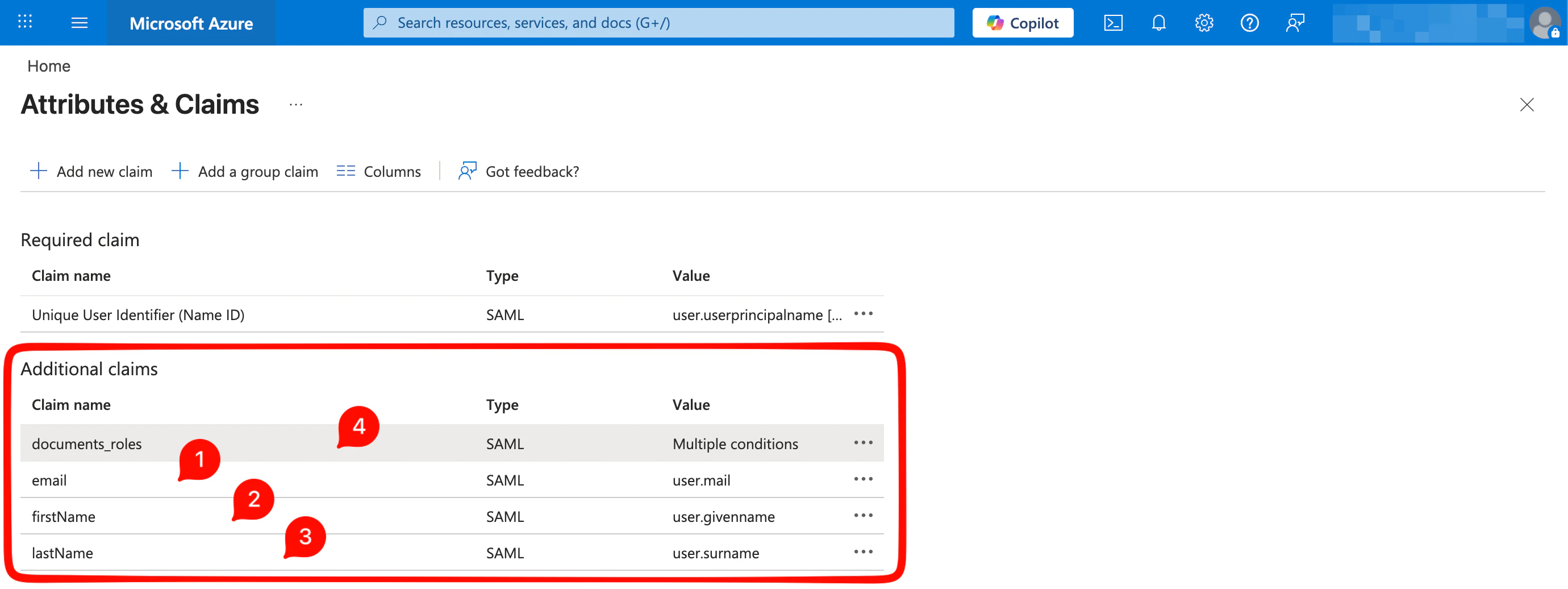
- In Attributes & Claims, update the default claims so they match the table above. For each required claim:
- Set Name to the claim name shown in the table, for example
email - Clear the Namespace field
- Set Name format to
Omitted (default) - Set Source to
Attribute - Select the correct Source attribute, for example
user.mailAfter the changes, the Additional claims section should look similar to the example below:
- Set Name to the claim name shown in the table, for example
- Optionally, add a claim named
documents_rolesto control which customer tenant the user can access and which role should be assigned in the Resistant AI platform. Each value should combine:- A tenant identifier, preferably the tenant ID provided by Resistant AI
- A separator, for example
_ - A user role code Supported role codes:
RW= Read-WriteRO= Read-Only Exampledocuments_rolesvalues:"documents_roles": ["tenant1_RW"]"documents_roles": ["tenant1_RO", "tenant2_RW"]"documents_roles": ["29Z73Z5p2ECTsEdCzGA0AlpiaXQ_RW", "2w5buuFoVCn9dySYnsqedMkVI8N_RW", "29Z74Z5p2ADTsEdCyGA1AlpiaXQ_RW"]
- After you complete this step, your Microsoft Entra ID configuration is ready. Resistant AI can complete the remaining configuration on the service provider side after receiving your identity provider metadata.
Step 5 — Send Microsoft Entra ID metadata to Resistant AI
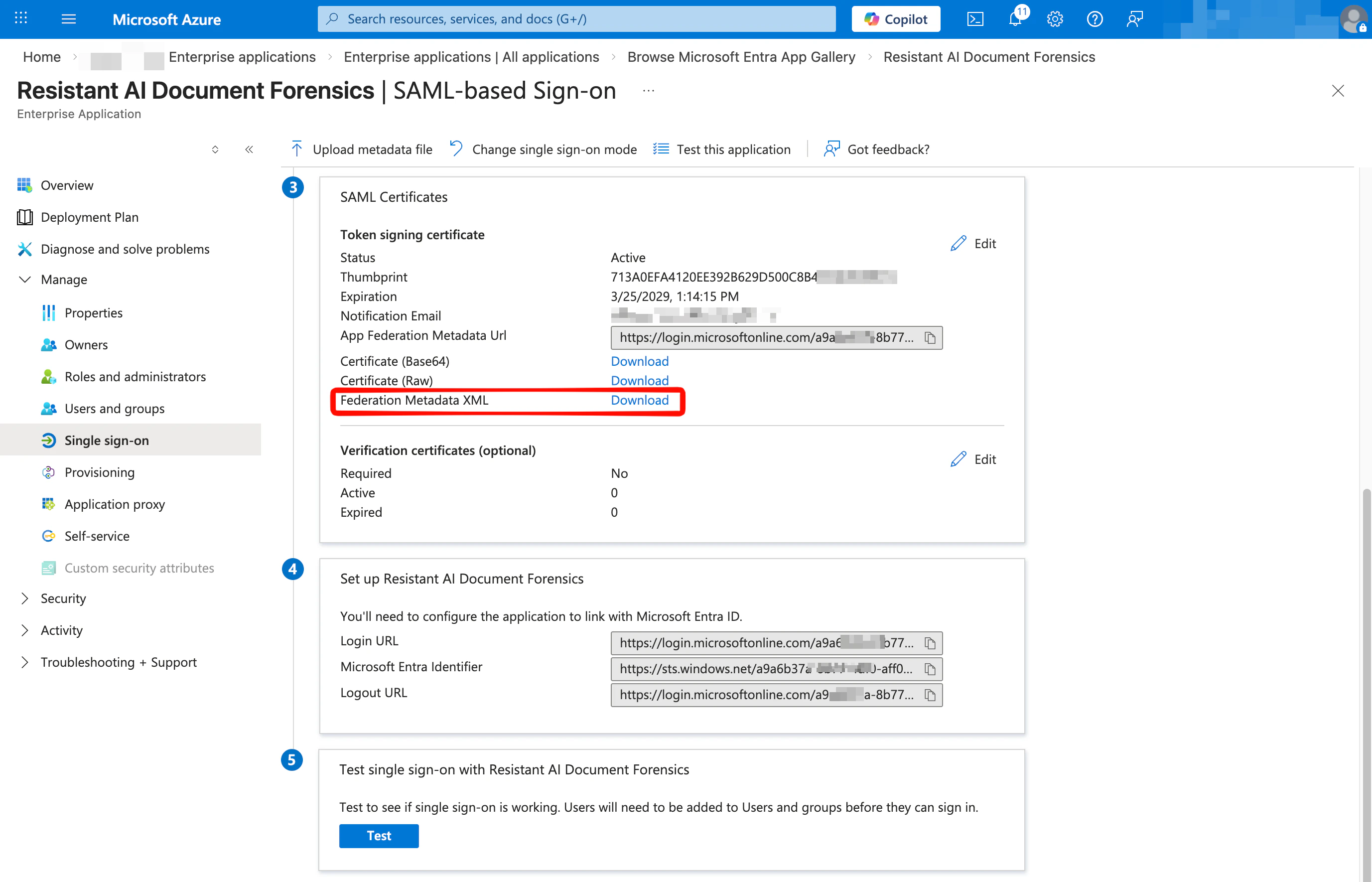
On the SAML-based Sign-on page, in the SAML Certificates section:- Download the Federation Metadata XML file.
- Send the file to Resistant AI.
Step 6 — Wait for Resistant AI to complete the configuration
Resistant AI will finalize the Service Provider configuration and confirm when the integration is ready for testing.Step 7 — Test the SSO integration
Before testing:- Assign a test user in Microsoft Entra ID to the new enterprise application.
- Make sure the test user can access the following URLs from a web browser:
- Your Microsoft Entra ID sign-in page, for example
https://login.microsoftonline.com/... - Your Resistant AI Document Forensics Web UI URL, for example
https://<NAME>.documents.resistant.ai - Resistant AI Identity and Access Management (IAM) URL:
https://eu.id.resistant.ai
- Your Microsoft Entra ID sign-in page, for example
- Ask the test user to open the Resistant AI Document Forensics UI URL in a browser and confirm that:
- the user is redirected to Microsoft Entra ID for authentication
- after sign-in, the user is redirected back to the Resistant AI application successfully
- If the test user is also an administrator with access to this SSO configuration, use the built-in test function on the SAML-based Sign-on page.
SSO messages pass through the user’s browser. Browser developer tools and a SAML tracer are usually the fastest way to debug.
Notes and tips
- Email address changes
The email address received in the SAML claim is the primary user identifier. If it changes, the user may be treated as a new identity. - Maximum SSO session lifetime
12 hours - Idle SSO session timeout
2 hours - Supported SAML bindings
HTTP POST (preferred) and HTTP Redirect - SAML debugging tool
Use the SAML-tracer browser extension for Chrome and other Chromium-based browsers or Firefox - Supported SSO flow
SP-initiated only. The SSO flow starts when the user opens the Resistant AI Web UI URL. - IdP-initiated sign-in
If the SSO flow is started directly from the identity provider without opening the Web UI URL, and no Sign-on URL is configured, the user may be redirected to the Resistant AI Okta dashboard instead of the Document Forensics application. This page is useful for checking account details and recent activity, but it is not the main application entry point. The page is available at https://eu.id.resistant.ai/account-settings/home.
Next steps
- Generic SAML overview: SSO setup (SAML 2.0)
- OIDC alternative: SSO setup (OIDC)